Advanced Encryption Standard, commonly known as 256-bit AES encryption, can be a data/file encryption security technique that uses a 256-bit key to encrypt and decrypt data or files. It is one of the most reliable encryption algorithm techniques.
The Advanced Encryption Standard (AES) is a symmetric block cipher picked from the U.S. federal government to protect classified details. AES is employed in hardware and software throughout the world to encrypt sensitive info. It’s necessary for federal government monitor security, cybersecurity, and electronic data protection.

The Advanced Encryption Standard was created by Just Two Belgian cryptologists, Vincent Rijmen and Joan Daemen. The pair had created a cipher named Rijndael plus they accommodated this to shape AES. The need for AES was identified by the US National Institute for Standards and Technologies (NIST). The Institute was tasked with defining a secure encryption program that may be utilized by the US government and all of its own agencies.
How does AES encryption work?
AES includes three block digits: AES-128, AES-192 and AES-256.
AES- uses a 128-bit key length to encrypt and decrypt a block of messages, even whilst AES-192 utilizes a 192-bit key length and AES-256 that a 256-bit key length to encrypt and decrypt messages. Every single and every cipher encrypts and decrypts data in blocks of 128 pieces employing cryptographic keys of 128, 192, and 256 bits, respectively.
Symmetric, also known as a secret key, ciphers use exactly the identical key for encrypting and decrypting, so the sender and the receiver should know — and use — even exactly the same secret key. The government classifies advice into about 3 groups: Confidential, Secret or Top Secret. All key lengths can be used to safeguard the Confidential and Object level. Key information requires either 192- or 256-bit important lengths.
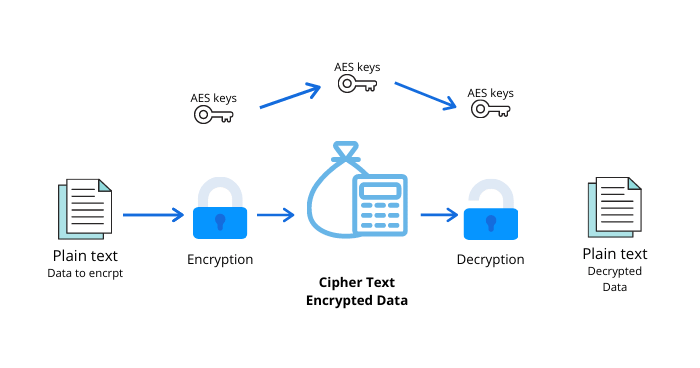
The AES encryption algorithm defines numerous transformations which are to be done on data stored in a variety. The very first thing of the cipher will be to place the information into a range — after that, the cipher transformations are replicated over numerous encryption rounds.
The first conversion from the AES encryption cipher is the substitution of info utilizing a substitution table; the instant conversion alters data columns and the 3rd combinations columns. The previous modification is performed on each individual column using another part of the encryption key. Longer keys demand more rounds to finish.
Can AES be cracked, How safe it is?
To better comprehend that to simple words, it would take billions of years using current computing technology to brute force an AES higher-level encryption cipher. If you should be a hacker, it really is perhaps not really worth striving.
AES 256-bit encryption symmetric keys to guard customers’ sensitive data so that no government, bureaus, or hackers may snoop into the info. Actually, if someone wants to force, it is going to take 13.8 billion years to crack. Experience this specific bank-grade encryption to maintain your online anonymity and secure your own data.
The difference between AES-128 vs AES-256
In general, stability experts think that AES is protected against brute force attacks, that examine every potential key blend before the right key can be located. Nevertheless, the essential size utilized for security has to become significant enough that modern computers find it impossible to crack that, despite having Moore’s Law advances in chip rate.
256-bit encryption crucial is a whole lot more difficult to imagine for brute-force attacks than a 128-bit key nevertheless, as the latter requires as long to guess, despite enormous computational ability, that is not likely to be an issue for the foreseeable future as a hacker would want to make use of quantum computing to generate the necessary brute-force.
But, 256-bit keys require also far a lot much additional processing capacity and can simply just take more time to execute. When electricity can be a problem, notably on devices that are small, or at which latency may be a problem, 128-bit keys are somewhat more inclined to become the optimal/optimally choice.
When hackers want to obtain access to a platform, they are going to plan for the weakest level, and it is often not encryption, whether the secret would be 128-bit or even 256-bit. Clients will want to be certain the software involved does exactly what they really need it to do, so it safeguards user info not surprisingly, and that the entire process has no weak points.
Additionally, there shouldn’t be any grey locations or doubt about information processing and storage. As an instance, in the event the info is from the cloud, then users will want to be familiar with positioning of this cloud. Most of all, the stability applications you select ought to be simple to work with so users do not need to use dangerous workarounds to receive their tasks done.
VPN those providing AES-256 Encryption
AES is used by all of the major VPN providers, some of them listed blow
- ExpressVPN
- IPVanish
- Surfshark
- StrongVPN
- PureVPN
- VyprVPN
- CyberGhost
- ZenMate
- HideMyAss
- NordVPN
- Fast VPN
Why should you encrypt your online data?
Encryption is essential since it makes it possible for you to securely safeguard data you don’t want anyone to get access to. Companies put it to use in order to shield corporate keys, the government uses it to protect classified information to safeguard confidential and secret files, and lots of men and women put it to use to protect personal information from matters like identification theft.
You can even use encryption to safely protect folder contents, which could comprise emails, chat histories, taxation info, credit card numbers, or some sensitive details. In this manner, even though your laptop is stolen, then that data is still safe.
Is Encryption necessary?
In the present modern occasions, cyber-attacks and statistics breaches have become common. With massive data hacks and secret details from the open, AES encryption is your best buddy. Encryption using AES will keep your emails confidential, health documents secure, banking transactions protected, and also social security number masked away from identity thieves, and also so much more. For best encryption, you must have a good VPN provider.
Best VPN Provider
